The security of 3D printers jeopardized by… the noise they make!
A surprising study confirms it: the sounds and vibrations of 3D printers would give out crucial information on the source code of printed objects. The study was lead by professor Mohammad Al Faruque, integrated cyber-physical systems specialist from the university of California in Irvine. It demonstrates that vibrations and acoustic signals made by machines allow you to precisely trace the movements of the nozzle and convey information on the source files such as the G-code, thus allowing the reconstitution of the printed object.
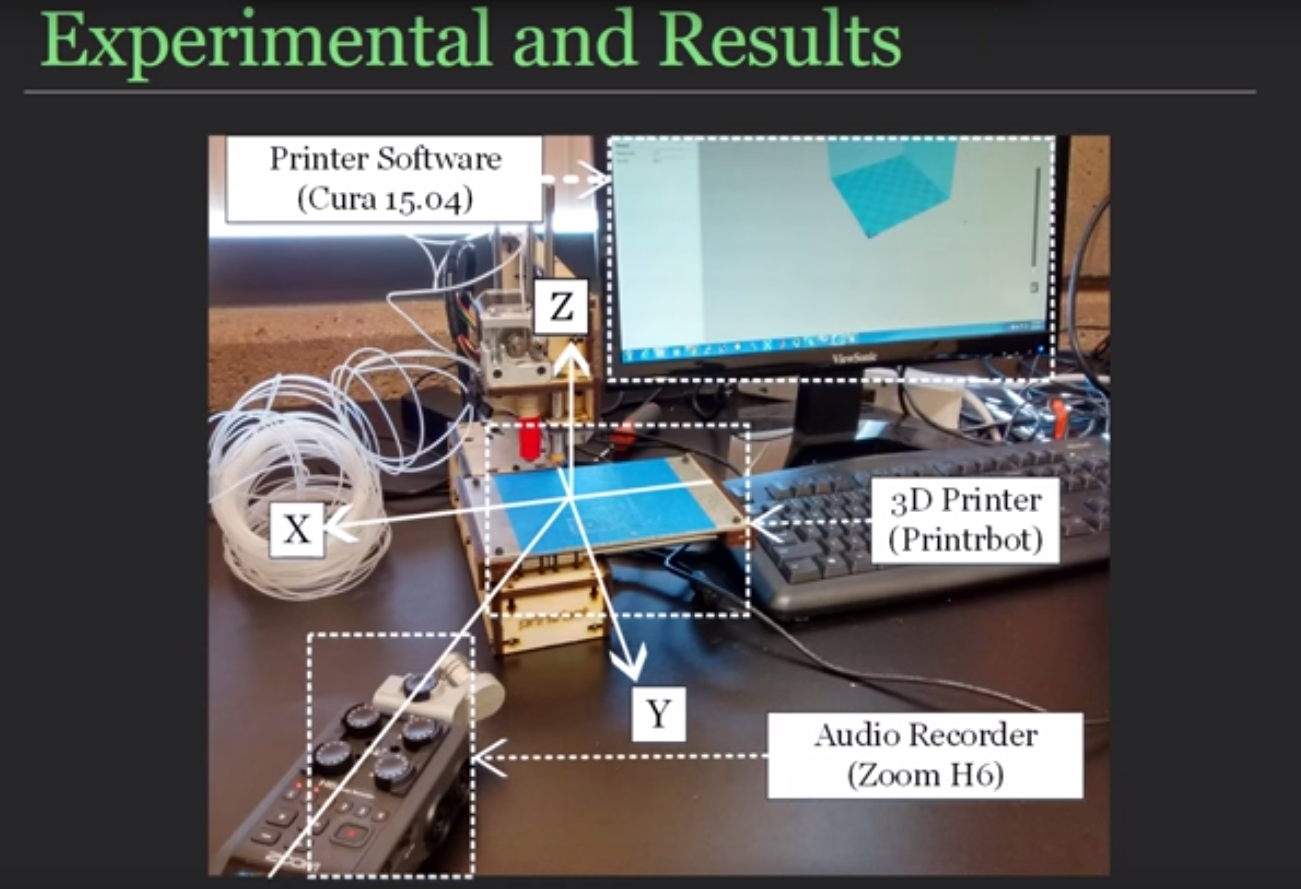
“An assailant motivated by industrial espionage purposes can violate the confidentiality of the system to manipulate its intellectual property”, shows this report that demonstrates that acoustic emissions of 3D printers contain a wealth of sensitive information. To prove their point, the researchers simulated an attack by using a Zoom type recorder–although a simple mobile phone will do the trick–positioned close to a 3D printer. The recorded sounds were then analyzed by algorithms to extract the specific information of the G-code. In the end, professor Al Faruque’s team was able to reproduce a test object and its code with a precision level close to 90%. “This work serves as proof of concept giving evidence of the vulnerability of additive manufacturing systems”, concludes this study that is likely to make more than one manufacturer shudder.
Presentation video of the experience:
